Risk Management Enterprise - Truths
Wiki Article
The Ultimate Guide To Risk Management Enterprise
Table of ContentsRisk Management Enterprise Things To Know Before You BuyNot known Factual Statements About Risk Management Enterprise The Ultimate Guide To Risk Management EnterpriseHow Risk Management Enterprise can Save You Time, Stress, and Money.Indicators on Risk Management Enterprise You Need To KnowThe 3-Minute Rule for Risk Management EnterpriseSome Known Details About Risk Management Enterprise
Below are several of its crucial functions that facilities must know. So, take an appearance. Real-Time Danger Assessments and Reduction in this software program enable organizations to constantly keep track of and evaluate dangers as they evolve. This attribute leverages real-time data and automated analysis to determine possible threats immediately. Once dangers are identified, the software application facilitates instant reduction activities.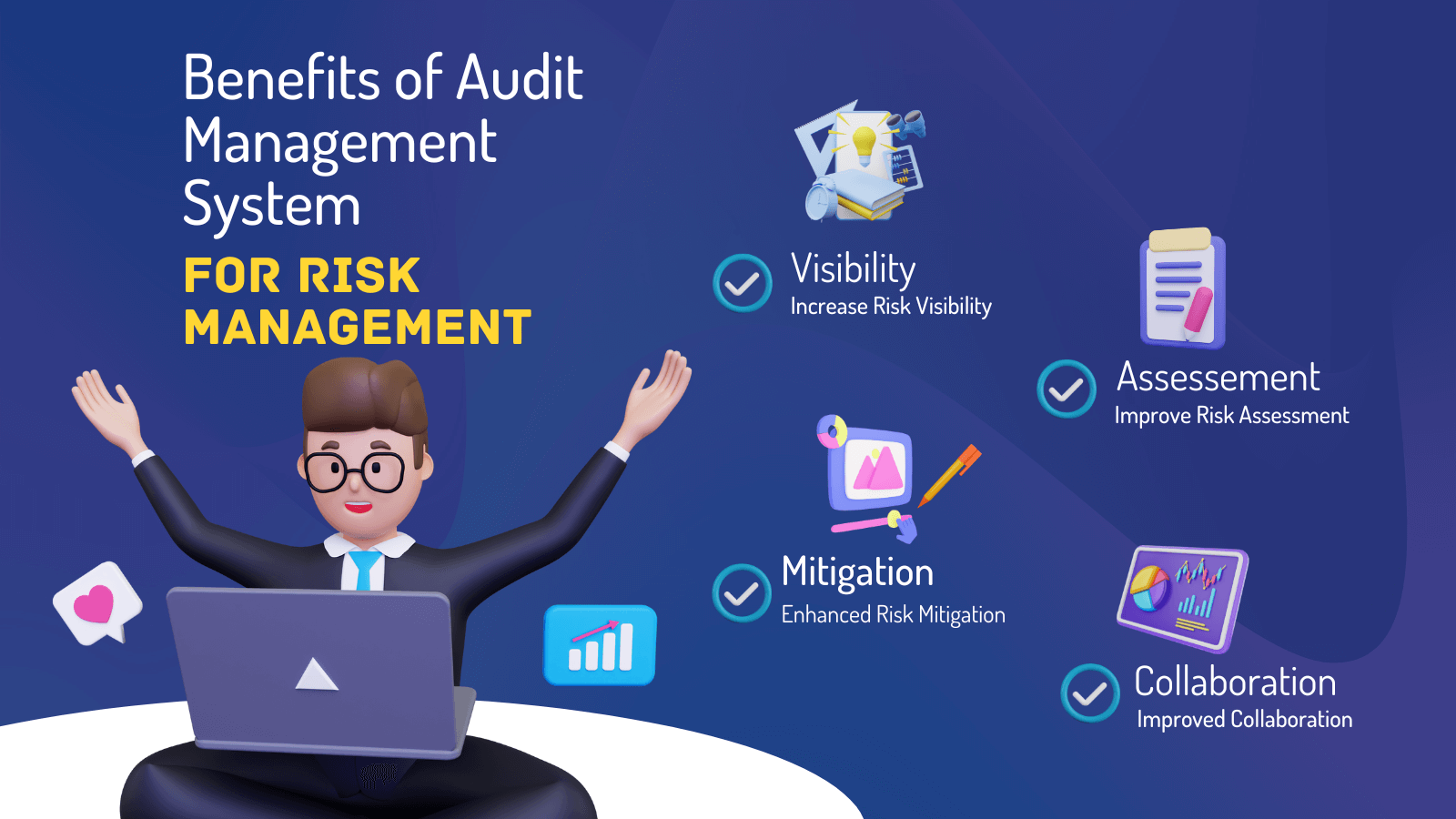
KRIs resolve the trouble of irregular or vague danger assessment. They deal with the obstacle of continuous risk monitoring by offering tools to monitor threats constantly. KRIs improve security danger oversight, guaranteeing that possible dangers are identified and handled effectively. The job of risk monitoring ought to not be an obstacle. Organizations need to rely on an excellent and sophisticated threat management software program.
7 Easy Facts About Risk Management Enterprise Described
IT risk management is a part of venture threat management (ERM), developed to bring IT run the risk of according to an organization's threat cravings. IT run the risk of administration (ITRM) includes the policies, treatments and modern technology essential to lower dangers and susceptabilities, while keeping conformity with suitable regulative requirements. In addition, ITRM seeks to restrict the effects of harmful occasions, such as safety and security breaches.While ITRM frameworks provide beneficial support, it's easy for IT groups to deal with "framework overload." Veronica Rose, ISACA board supervisor and an info systems auditor at Metropol Corp. Ltd., advises the use of a combination of frameworks to attain the very best results. The ISACA Threat IT framework straightens well with the COBIT 2019 framework, Rose said.
Business Threat Administration Software Growth: Perks & Features, Expense. With technological developments, threats are constantly rising. That being stated, companies are more probable to encounter challenges that influence their finances, procedures, and track record. From swiftly changing markets to governing adjustments and cyber risks, organizations navigate with a frequently altering sea of threats.
The smart Trick of Risk Management Enterprise That Nobody is Talking About
In this blog, we will dive into the world of ERM software application, exploring what it is, its benefits, features, etc so that you can build one for your organization. Venture Threat Monitoring (ERM) software program is the application program for preparation, guiding, organizing, and regulating organization tasks and enhancing danger administration processes.With ERM, organizations can make informative decisions to improve the overall strength of business. Read: ERP Application Advancement Dedicated ERM systems are essential for companies that frequently take care of huge amounts of delicate info and multiple stakeholders to accept calculated choices. Some industries where ERM has actually ended up being a conventional system are healthcare, financing, construction, insurance, and info modern technology (IT).
It can be avoided by utilizing the ERM software system. This system automates policy conformity monitoring to maintain the company safe and compliant.
The 6-Second Trick For Risk Management Enterprise
You can likewise link existing software program systems to the ERM through APIs or by including information by hand. Businesses can make use of ERM to review threats based upon their prospective influence for much better threat management and mitigation.: Adding this feature allows individuals to obtain real-time alerts on their devices regarding any threat that could happen and its impact.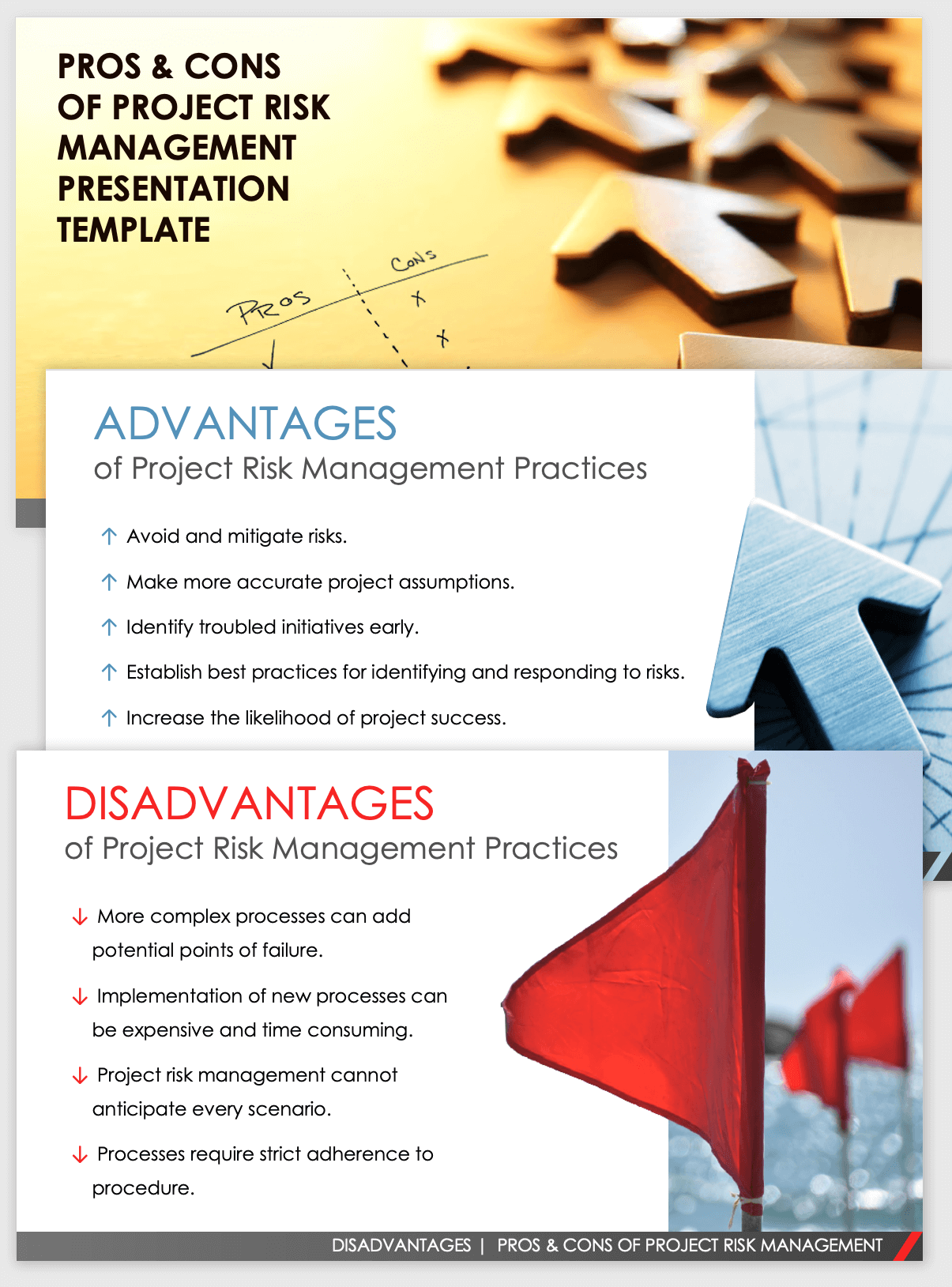
Instead, the software program enables them to establish limits for various procedures and send out push notices in instance of feasible threats.: By integrating data visualization and reporting in the customized ERM software application, organizations can obtain clear insights regarding danger trends and performance.: It is mandatory for organizations to follow sector compliance and regulatory criteria.
These systems enable firms to carry out best-practice risk administration procedures that straighten with sector standards, offering an effective, technology-driven method to determining, analyzing, and mitigating threats. This blog site checks out the benefits of computerized risk administration devices, the locations of risk management they can automate, and the value they bring to a company.
Fascination About Risk Management Enterprise
Teams can set up types with the relevant areas and conveniently develop various types for various risk types. These threat evaluation kinds can be circulated for conclusion through automated operations that send alerts to the appropriate team to complete the kinds online. If forms are not completed by the deadline, then chaser e-mails are automatically sent out by the system.The control tracking and control testing procedure can also be automated. Companies can make use of automated operations to send regular control examination alerts and staff can go into the outcomes via on the internet kinds. Controls can likewise be checked by the software by setting rules to send informs based on control data held in various other systems and spreadsheets that is drawn into the system via API combinations.
Threat management automation software program can also support with danger coverage for all degrees of the business. Leaders can watch records on risk exposure and control effectiveness via a selection of reporting outputs including static records, Power BI interactive records, bowtie evaluation, and Monte Carlo simulations. The capacity to draw actual time records at the touch of a button cuts out difficult data control jobs leaving risk groups with even more time to assess the information and encourage business on the very best strategy.
Organizations operating in affordable, fast-changing markets can not pay for delays or inadequacies in attending to prospective dangers. Conventional threat administration using manual spreadsheet-based procedures, while familiar, frequently lead to fragmented information, lengthy reporting, and a raised probability of human error.
Risk Management Enterprise Fundamentals Explained
This makes certain risk registers are constantly current and lined up with business objectives. Conformity is an additional vital driver for automating threat management. Specifications like ISO 31000, CPS 230 and COSO all give guidance around risk administration ideal techniques and control frameworks, and automated danger administration devices are structured to align with these demands assisting companies to fulfill most commonly utilized threat monitoring standards.Search for danger software program systems with a consents power structure Learn More Here to conveniently establish workflows for risk acceleration. This performance allows you to customize the sight for each and every customer, so they just see the data appropriate to them. See to it the ERM software supplies user tracking so you can see who entered what information and when.
Look for out tools that supply job threat administration capacities to manage your projects and profiles and the connected risks. The benefits of embracing risk monitoring automation software expand far past performance.

How Risk Management Enterprise can Save You Time, Stress, and Money.
While the you can look here case for automation is engaging, applying a threat monitoring platform is not without its difficulties. To overcome the difficulties of danger management automation, organizations need to invest in information cleaning and administration to make certain a strong structure for implementing an automated system.Automation in threat administration empowers businesses to transform find here their method to run the risk of and develop a more powerful foundation for the future (Risk Management Enterprise). The inquiry is no much longer whether to automate threat management, it's how soon you can begin. To see the Riskonnect at work,
The solution often exists in how well threats are prepared for and taken care of. Job monitoring software application serves as the navigator in the turbulent waters of job execution, offering devices that determine and analyze risks and design methods to reduce them properly.
Report this wiki page